Broadcom has released Carbon Black Threat Tracer, an intuitive tool that enables threat analysts to visualise connections between any objects.
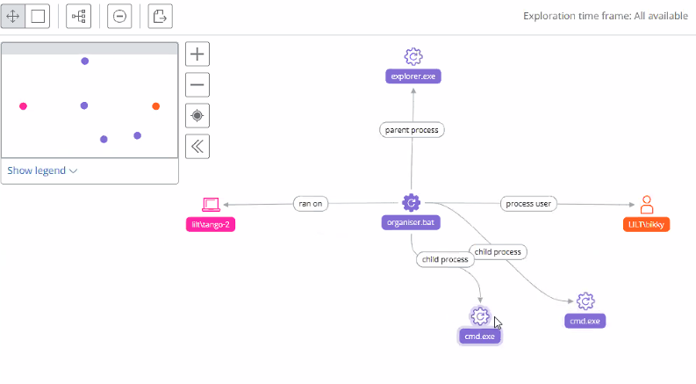
Any objects (e.g. hash, endpoint, user, process, etc.) from Carbon Black EDR can be placed on a whiteboard-like interface, and the connections between them are displayed automatically.
Included in every Carbon Black Cloud Enterprise EDR subscription
Threat Tracer does not focus on hierarchical or causal views, but rather on the relationships between entities such as devices, processes, files, registry keys, users, hashes, IP addresses, or domains. This powerful tool for visual threat data analysis goes far beyond traditional causal process trees.
This relationship view, which graphically maps the threat or attack and all affected entities, enables teams to quickly assess the impact of a threat. This broader perspective allows analysts to consider the entire context before remediating the threat, rather than acting during remediation and potentially alerting the attackers. Visualising the threat allows remediation teams to identify attack points they can use to stop or contain the attack without warning the attacker.
See more, stop more
Threat Tracer streamlines analysis by enabling security teams to dynamically explore incidents and quickly identify and visualise the scope of a particular threat. Analysts can conduct precise, organisation-wide investigations across all devices monitored by Carbon Black Cloud. Use cases include:
- Malicious IP address. An analyst identifies a suspicious process and uses Threat Tracer to investigate the associated file, parent process, and affected devices. Result: The analyst obtains a visual overview of all devices running the malicious process, facilitating remediation prioritisation and revealing the threat’s overall impact.
- Unusual user access. An analyst notices that a user has logged into a device they should not access or do not usually access. Threat Tracer helps explore all devices the user has logged into. Result: Security teams can identify and block potentially problematic device accesses while obtaining a visual overview of suspicious user activity.
- Threat hunting. An analyst actively searches for abnormal patterns that may indicate emerging attacks. Result: The analyst can detect and stop attacks before they cause damage.
- Investigation and triage. An analyst gains full context around specific entities within an environment, helping determine cause and effect of suspicious events and understand their impact on the environment.
Broadcom releases Carbon Black Threat Tracer…
Immediately after acquiring VMware, Broadcom migrated the Carbon Black Cloud solutions to Google Cloud. This is important because all other Broadcom security solutions are already running there. In the medium term, Carbon Black EDR will be available in the central Symantec Enterprise Cloud console, and in the long term, Broadcom’s EDR solutions will be consolidated.
Further articles on this topic: